Python Developers Warned Of Trojanized PyPI Packages Mimicking Popular Libraries
Cybersecurity researchers are warning of "imposter packages" mimicking popular libraries available on the Python Package Index (PyPI) repository.
The 41 malicious PyPI packages have been found to pose as typosquatted variants of legitimate modules such as HTTP, AIOHTTP, requests, urllib, and urllib3.
The names of the packages are as follows:
aio5, aio6, htps1, httiop, httops, httplat, httpscolor, httpsing, httpslib, httpsos, httpsp, httpssp, httpssus, httpsus, httpxgetter, httpxmodifier, httpxrequester, httpxrequesterv2, httpxv2, httpxv3, libhttps, piphttps, pohttp, requestsd, requestse, requestst, ulrlib3, urelib3, urklib3, urlkib3, urllb, urllib33, urolib3, xhttpsp
"The descriptions for these packages, for the most part, don't hint at their malicious intent," ReversingLabs researcher Lucija Valentić said in a new writeup. "Some are disguised as real libraries and make flattering comparisons between their capabilities and those of known, legitimate HTTP libraries."
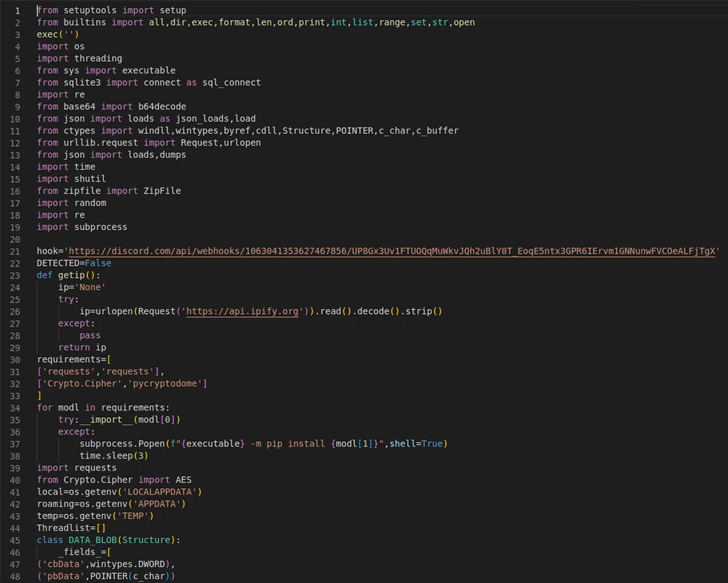
But in reality, they either harbor downloaders that act as a conduit to deliver second-stage malware to infected hosts or information stealers that are designed to exfiltrate sensitive data such as passwords and tokens.
Fortinet, which also disclosed similar rogue HTTP packages on PyPI earlier this week, noted their ability to launch a trojan downloader that, in turn, contains a DLL file (Rdudkye.dll) packing a variety of functions.
The development is just the latest attempt by malicious actors to poison open source repositories like GitHub, npm, PyPI, and RubyGems to propagate malware to developer systems and mount supply chain attacks.
The findings come a day after Checkmarx detailed a surge in spam packages in the open source npm registry that are designed to redirect victims to phishing links.
"As with other supply chain attacks, malicious actors are counting on typosquatting creating confusion and counting on incautious developers to embrace malicious packages with similar-sounding names by accident," Valentić said.
Source: thehackernews.com
 Reviewed by Zion3R
on
11:03 PM
Rating:
Reviewed by Zion3R
on
11:03 PM
Rating: