New Chinese Malware Attack Framework Targets Windows, macOS, And Linux Systems
A previously undocumented command-and-control (C2) framework dubbed Alchimist is likely being used in the wild to target Windows, macOS, and Linux systems.
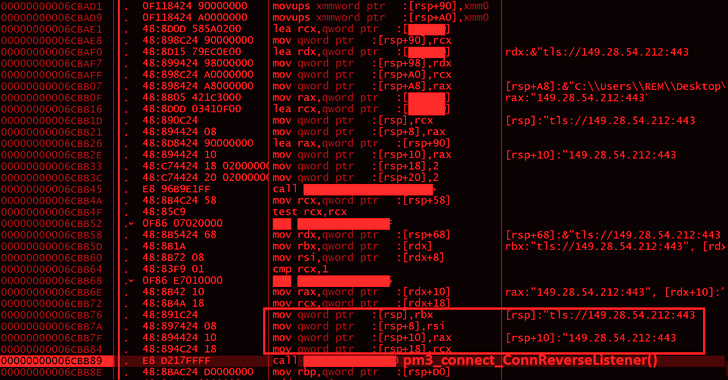
"Alchimist C2 has a web interface written in Simplified Chinese and can generate a configured payload, establish remote sessions, deploy payload to the remote machines, capture screenshots, perform remote shellcode execution, and run arbitrary commands," Cisco Talos said in a report shared with The Hacker News.
Written in GoLang, Alchimist is complemented by a beacon implant called Insekt, which comes with remote access features that can be instrumented by the C2 server.
The discovery of Alchimist and its assorted family of malware implants comes three months after Talos also detailed another self-contained framework known as Manjusaka, which has been touted as the "Chinese sibling of Sliver and Cobalt Strike."
Even more interestingly, both Manjusaka and Alchimist pack in similar functionalities, despite the differences in the implementation when it comes to the web interfaces.
Alchimist C2 panel further features the ability to generate PowerShell and wget code snippets for Windows and Linux, potentially allowing an attacker to flesh out their infection chains to distribute the Insekt RAT payload.
The instructions could then be embedded in a maldoc attached to a phishing email that, when opened, downloads and launches the backdoor on the compromised machine.
The trojan, for its part, is equipped with features typically present in backdoors of this kind, enabling the malware to get system information, capture screenshots, run arbitrary commands, and download remote files, among others.
What's more, the Linux version of Insekt is capable of listing the contents of the ".ssh" directory and even adding new SSH keys to the "~/.ssh/authorized_keys" file to facilitate remote access over SSH.
But in a sign that the threat actor behind the operation also has macOS in their sights, Talos said it uncovered a Mach-O dropper that exploits the PwnKit vulnerability (CVE-2021-4034) to achieve privilege escalation.
"However, this [pkexec] utility is not installed on MacOSX by default, meaning the elevation of privileges is not guaranteed," Talos noted.
The overlapping functions Manjusaka and Alchimist points to an uptick in the use of "all-inclusive C2 frameworks" that can be used for remote administration and command-and-control.
"A threat actor gaining privileged shell access on a victim's machine is like having a Swiss Army knife, enabling the execution of arbitrary commands or shellcodes in the victim's environment, resulting in significant effects on the target organization," the researchers said.
Source: thehackernews.com
 Reviewed by Zion3R
on
6:12 AM
Rating:
Reviewed by Zion3R
on
6:12 AM
Rating: